Link Analysis and Timeline Analysis In Computer Forensics
What is Link Analysis?
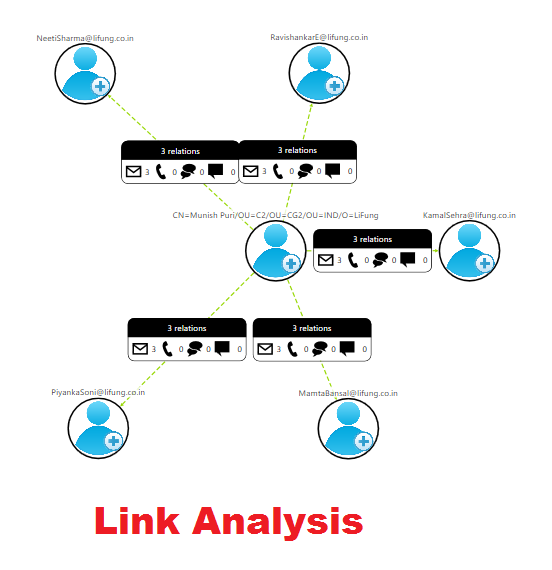
According to the definition, Link analysis is simply a data analysis method in the network theory to examine the connections or relationships between the network nodes. This connection or relationships can be between any type of nodes or objects like People, Organization, and transactions. Similar to the visual tool, this Link Analysis provides a powerful method that let users in understanding what is exactly happening very quickly.
Therefore, it is mostly used by many financial institutions like Banks and Insurance, Cyber Security agencies, to uncover the criminal networks. It also improves the fraud investigations, and find insiders frauds easily. In the same way, the government agencies perform link analysis to investigate frauds, improve the screening processes, investigate criminal activities, and to expose the terrorist network.
“Link Analysis basically helps examiners or investigators to create a visual picture of the communications between those who are involved in a criminal case.”
Use of Link Analysis Methodology
Link analysis is specially used to discover valuable knowledge, which used to visualize data in order to perform better analysis, mainly in the context of links i.e. Web links or relationship links between people or different entities. In addition, the relationship between the different identities will determine how these entities are associated with each other. Apart from all this, Link analysis is frequently used in search engine optimization, in intelligence, in market and medical research, and in security analysis.
In networking, the link analysis is done to determine the integrity of the connection between each node in the network after analyzing the data, which passes via the physical or virtual links. Using this data, the analysts will find the bottlenecks including all possible faulty areas and patch them up quickly in order to perform network optimization. The main three motive of Link analysis are:
- Identify matches for known the patterns of interests between the linked objects.
- Look for an abnormal condition by detecting profaned known patterns.
- Look for new patterns of interest.
How Can Link Analysis Be Performed?
There are many problems faced by the law enforcement agencies and intelligence analysts in identifying the relationships between the specific group of entities in the criminal network. In addition, this task can be really time-consuming and requires lots of efforts if done without any Link Analysis Software. Thus, to this in an effective manner, analysts can use any of the link analysis tool available in the market.
Introduction to Timeline Analysis
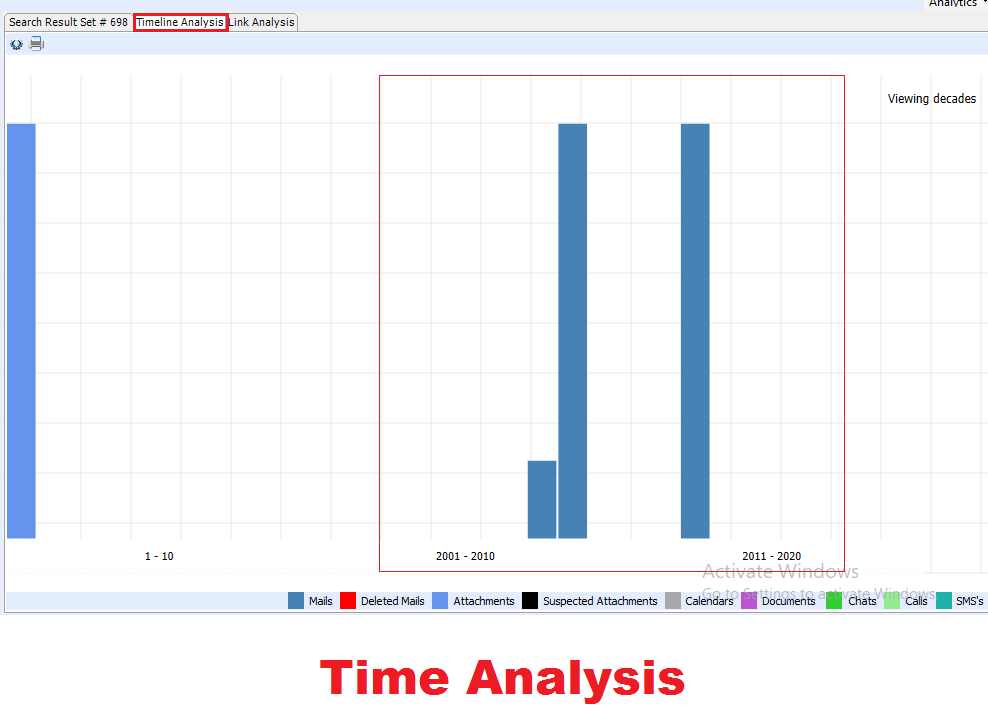
The timeline analysis is useful for performing a different type of investigations. It is mainly used to answer the questions related to when a system is used or what event occurs before or after a particular event. This is represented in Graphical form, which shows the number of event Moreover, it is very useful in digital forensics also to determine when a particular activity has occurred on a system. It identifies the data reduction and a particular state change on the system. In short, one can easily determine which event occurs at what and all other details related to that event.
Forensic Investigation: Perform Link and Timeline Analysis Effectively
In order to do Link and Timeline task with minimum efforts and more accurately, the investigators or analysts are advised to use Email Investigation Tool. This utility is capable to provide a visual representation of a criminal network also. It is one of the popular names in the field of digital forensics.
It keeps the track of all data transactions done through emails. One can easily use this tool to visualize, analyze, and investigate the wicked communication done between the suspects via Advance Link analysis algorithm with the software. It will easily detect the links between the suspects and also investigate the exchange of information and emails between them.Apart from all this, this Forensic Investigation tool also includes Timeline Analysis feature. This will let analysts determine when the particular event or data transaction has performed or occurred. In addition, this software also let users can email conversation between the users based on specific date, year, and decades.