Google Chrome Forensic Analysis: An Ultimate Path For Evidence Collection
It is a common and well known fact that the number of web users has increased nowadays. People spends their whole day infront of the computer and this clearly marks that large about of information will be there in the files related to the browsing. As since now many of the criminal activities are done with the help of information available in web, searching the browser file has become the important part of investigation. Or in other words, it is said that illegal activities are carried out with the help of web. Because of these, Google Chrome forensic analysis to examine files related to web become important. There are different browsers available for the users to surf over the web such as, Firefox, Chrome, Yahoo etc. Here, in this page you will get to know about how to collect artifacts from Google Chrome. The discussion covers all the related topics from where one can get the details.
Some of the areas in Google Chrome browser forensics that help investigators are as listed;
- History
- Cache
- Cookies
- Bookmarks
- Session restore file
- Current tabs
- Last session
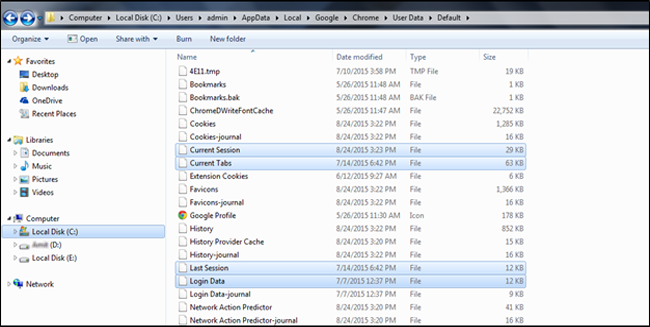
Let us start the evidence collection from ‘History’. But, where are the Chrome files located.
Location
History
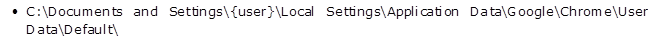
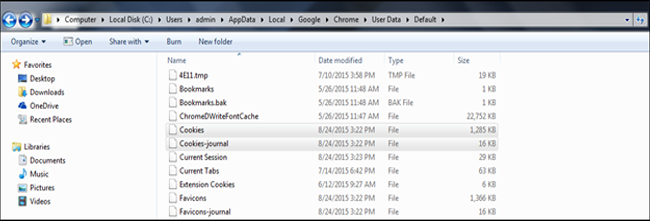
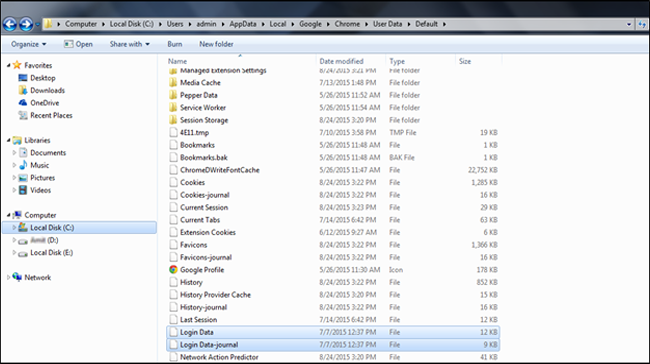
During Google Chrome forensic analysis, in the ‘History’, you will get to see all the sites visited so far and all the files follows Sqlite database file format.
Location of History:
In Windows XP
In Vista/7/8 and above;
From the ‘History’ file, you can view the ‘URLs’, ‘downloads’ and ‘visits’. It reveals the URLs visited, downloads made and the table of ‘visits lists the timestamps and type of visits thus, aids to the information collection easily.
Cache
In Google Chrome forensic analysis; Cache is the inevitable part since it contains the actual content of the message.
Location:
In Windows XP
Vista and above;
Cookies
Cookie stores the cookie information of the visited sites, includes site name, last time of the access of the cookie etc. Cookies are stored with ‘Cookies’ in Chrome and those cookies used with extension are stored in file called ‘Extension Cookies’.
Location of Cookies in Google Chrome forensic analysis;
Vista or Windows 7 or/and above;
In Windows XP
Where Does The Password Get Stored?
Apart from the history, cache, cookies etc., Chrome stores the login details in ‘Web Data’ file which is now replaced by ‘Login Data’ file. Moreover, the file stores IE7 Logins, auto complete entries, search keywords etc. Except the password, all the others are stored in text and passwords are encrypted by Triple DES algorithm.
In Vista and above Windows version, the location of ‘Login Data’ is;
Database
The location of database files is;
Windows XP
Vista and later
What More Can Be Seen?
While conducting Google Chrome browser forensics; for more probe, you can visit the sessions such as, Current Sessions, Current Tabs, Last Session and Last Tabs.
From the name of the files itself users will get to know about the use of the file. The last session file helps the users or the investigators to restore the last browsed session when the browser is opened up. While carrying out Google Chrome forensic analysis, these files are the way to collect the information regarding the opened tabs, about the sites exhibited etc.
Bookmarks
The bookmark specified by the users, if any will be stored in the ‘bookmarks’ and the file is located in;
Windows XP
Vista/7/8
With a thorough search over the Chrome files, an investigator can get the evidence for closing the case, if any. For a trained agent, finding the artifacts will be easier and now there are even tools available in the market to help in finding the evidence from these files. During Google Chrome browser forensics; if the locations are clear, one can find information easier. Hope this page has added some valuable information.