A Complete Guide to Digital Signature Technique in Cyber Security
The digital signature technique is a way to secure the document and guarantees that the contents of a message have not been changed in transit. When a user uses a digital signature in cyber security, then a simplex forensics hash function algorithm is added which makes the email message secure.
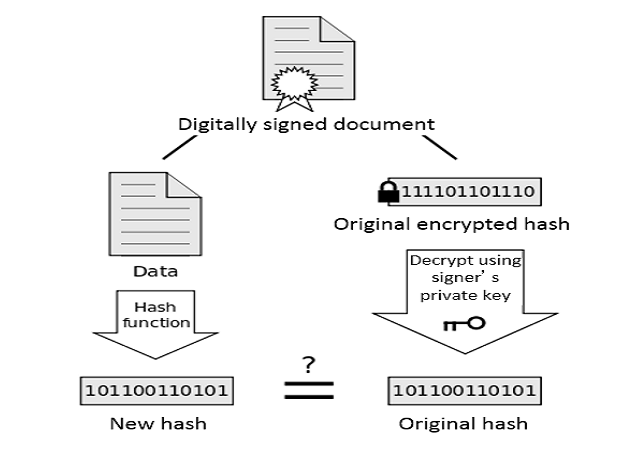
Only the recipient has access to scan and open the message. However, this digital signature strategy creates an encrypted message which can only be decrypted through the signer’s public key. The recipient, with the help of the signer’s public key, can validate the sender and the integrity of message contents.
After transmission, if a new hash value and the original hash value will not the same, then the recipient knows that someone changed the message.
What is the Key in Cryptography
The Key is a sequence of numbers that is generated randomly and is very complex and unique. There are two types of keys (digital signature: private key and public key) which are used to encrypt and decrypt the email message for digital signature in cyber security.
Public Key: Public-key cryptography provides integrity via digital signature and it is also used to encrypt email messages. Digital signature in public-key cryptography converts plain text into cipher-text which is very hard to read and interpret by the users.
Private Key: Digital signature private key encryption is used to decrypt the email messages, or we can say that the private key converts the cipher-text into a human-readable form.
If the message is encrypted by the public key, then with the help of the private key, the recipient can decrypt the message
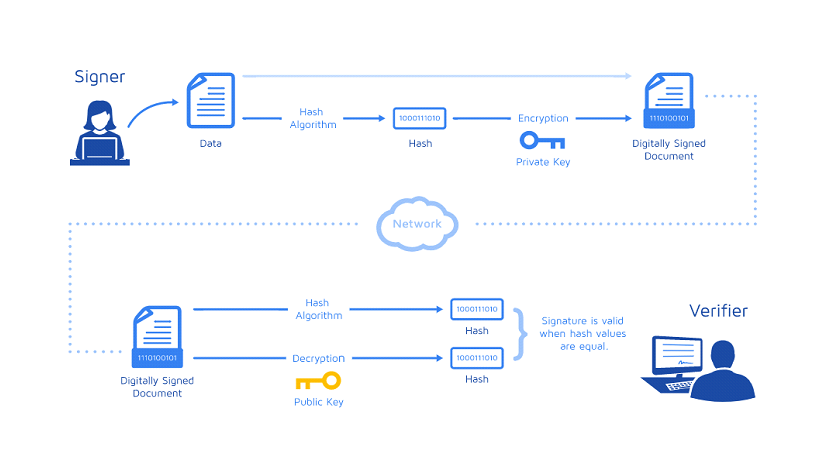
Working of Digital Signature
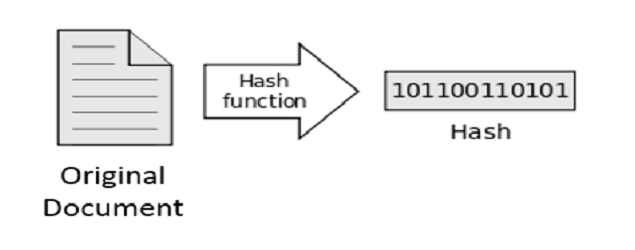
- When a user signs the document, a unique digital signature called hash is created. This hash value is unique for every message and if someone tries to change the message it would result in the different hash value.
- The new hash is encrypted by the private key of the signer. The encrypted hash value and the public key of the signer are combined into a digital signature.

- The digital signature is then transmitted along with the message.
- The receiver decrypt the digitally signed email message with the help of the public key of the signer.
- The program generates a new hash value for the message. If the new hash value matches the original hash value, the message has not been modified since the signature was applied.
Importance of Digital Signature Technique
- One of the main features of the digital signature is that it provides the highest level of security.
- Digital signature in cyber security is necessary for emails, it changes the structure, from a normal message into a coded message which maintains confidentiality.
- Digital signatures associate a signer, firmly with a document during recorded dealings.
- Digital signatures prune the danger of duplication or alteration of the document itself.
- Digital signatures make sure that signatures are verified, authentic and legit.
- Signers are supplied with PINs, passwords, and codes which will certify and verify their identity and approve their signatures.
Types of Digital Signature in Cyber Security
There are primarily three types of digital signature certificates: Class-1, Class-2 & Class-3 each having altogether different levels of security. All the authorized signatories of the company want the Class-2 digital signature certificate.
Various Forms of Digital Signatures
Adding a certifying signature to a document indicates that the user is an author and need to secure the document against any alteration. It additionally contains the name of the document signer and therefore the certificate issuer point the authorship and edibleness of the document.
Several platforms that permit different types of digital signature such as:
Adobe supports approval digital signatures, Microsoft Word supports visible and non-visible digital signatures
Approval Signatures
Approval signatures on a document are used in the organization’s business advancement. They help to optimize the organization’s approval procedure. The process involves capturing approvals created by a user and alternative people and embedding them at intervals. Adobe permits signatures to include details such as an image of your physical signature, location, date, and other official seals. These alter one user or multiple users to digitally sign one document.
Visible Digital Signature Technique
This enables one or multiple users to digitally sign one document. A visible signature includes information that holds a noticeable marker, once viewing the document, showing that it’s been signed.
Invisible Digital Signatures
Invisible digital signatures do not show your signature in the document. However, it produces indications of the credibility, integrity, and origin of the document.
Advantages of Digital Signatures
Using the digital signature in cyber security has several advantages:
- Sending documents digitally is very fast and efficient.
- Clients will sign documents with any internet-enabled device.
- Since the documents are saved within the cloud, so clients can access and sign documents anytime.
- It works fast wherein the client will sign and return the documents in few simple clicks.
- Also, the transactions are very secure, enforceable, auditable, and accepted in most of the countries.
- Users can see who opened the document.
- An audit path is employed to make sure the confidentiality of all transactions.
- Online signatures are accepted by investigators and may be used in court as a piece of evidence.
Conclusion
In many countries, the digital signature in cryptography is used for security purposes. As an example, the United States government authenticates the digital versions of documents using a digital signature. The rise in data alteration incidents has caused a serious upward trend as well as the acceptance of the digital signature in cyber security. In digital forensic, investigators analyze email messages through third-party software such as MailXaminer Email Analysis Tool. This software has advanced functionalities, it generates hash values of every email message which are further used to verify the integrity of that message.