Use of MD5 and SHA1 Hashing Algorithm In Digital Forensics
The internet world is full of spammers and hackers that wish to change, edit or delete data being transmitted. In other occasions, some bits may get affected by an external factor like electromagnetic fields surrounding a cable. There is no guarantee that the receiver will get the exact message without any alteration. This post talks about what is MD5 and SHA1 and hashing algorithms. It is a method to ensure secrecy and make sure that the correct data is received at the other end. It dwells deeper into this topic to understand its need in the world of forensic analysis and truth finding. Keep on reading to find out more.
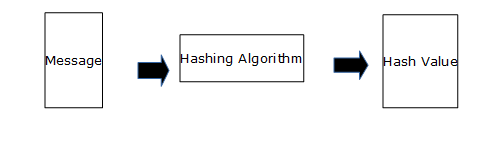
What is Hashing?
It is an act of applying a mathematical function of arbitrary length to the original text. Produce a shorter fixed-length value or key called hash value or message digest, used for faster accessing of data from a storage or for security purposes.
Hash Function Definition
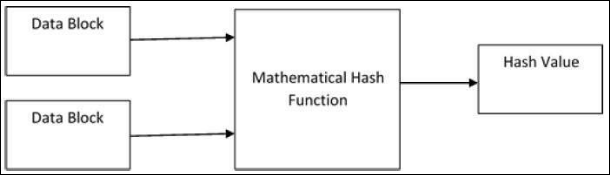
These are mathematical operations h that take Input X and produce Output h(x). It compresses the data into smaller representation and gets a name digest. They typically take two fixed-size blocks of data ranging from 128 to 512 bits to create a hash sum.
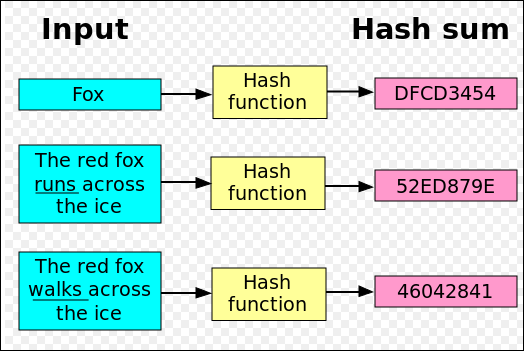
How Does Hashing Work?
The message is broken down into blocks of bytes. These act as input to a binary operation that takes two value. One is a predefined string and the other is the original text. It produces a fixed-length string as output. Each data block varies depending on the algorithm.
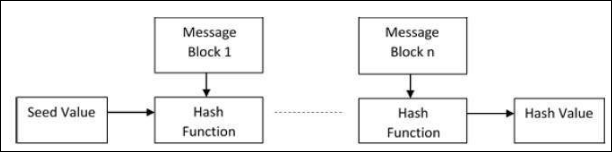
What is Hashing Algorithm?
It is a set of instructions that repeats the hashing process for each data block. It takes a combination of the most recent message block and last output and performs a hash operation. This way, the first hash value becomes input to the second hash operation and second to third and so on.
What are the Types of Hashing Algorithm?
Following are two main techniques of securing messages during transfer:
MD5: It is a one-way function that produces a digest form of information in size of 128 to 160-bit. It also helps verify data integrity and possible corruption by comparing hash values. It is faster but a lot less secure. MD5 hashing algorithm can be easily cracked by hackers and has a lot of limitations including collision. This is where more than one input text produces the same output.
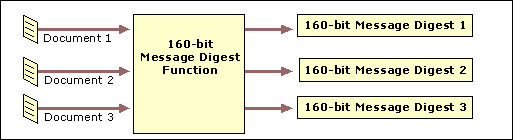
SHA1: It is short for Secure Hashing Algorithm with produces a hash value of size 160-bit. This is comparatively longer in length and difficult to break and get the original string. This is used by many big companies to compare password in their store with one typed by the user.
Applications of MD5 and SHA1 Hashing Algorithm
Listed here are some of the common ways for which these hash functions are quite commonly known for:
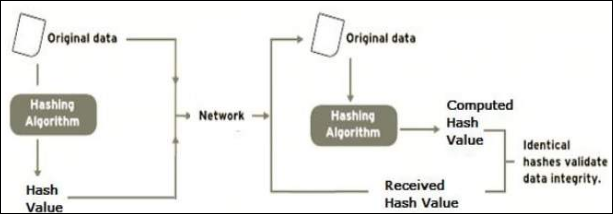
Data Integrity Check: This is the most application of hashing algorithm. A checksum is generated on ISO files by the developer and published on their website. The user does the same on their system and compares results. This can be used for verifying downloads and validate that original documents are received. It is also helpful in detecting any changes in data upon download. It also checks for any misplaced byte during transfer of important files.
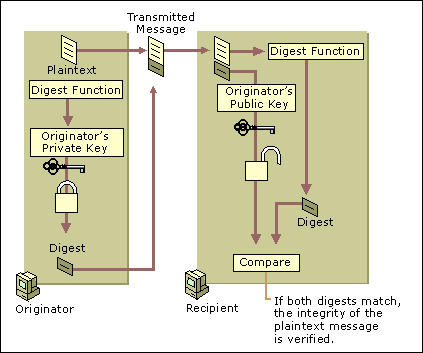
Validating Emails at Recipients End: The application of message digest includes verifying that correct data is received. The originator creates a hash value using a digitally signed private key and sends it across. The recipients check it at their end by decrypting the message using the public key. Then, creates a digest on their system and compares with the original value. Following is a diagrammatic representation of the same:
Conclusion
Professional Investigator and Expert users always want to make sure what they are spending money on Email Forensic Tool that can help them to view the hash value of the information, so that compare the values while forensic email investigation of different email clients. This post can be used for reference to know all about what is MD5 and SHA1 and what they are used for. It explains in detail all there is to know about the two hash function. It goes on to mention its practical application in everyday usage. One can gain a lot of knowledge by just going through this page.